Network+ Guide to Networks: A Comprehensive Overview (Updated 04/15/2026)
This guide, updated today, 04/15/2026, provides a foundational understanding of networking, leveraging resources like NetworkChuck on YouTube for a comprehensive learning experience.
Networking is the backbone of modern communication, connecting devices globally and enabling seamless data exchange. Understanding these fundamentals is crucial, and resources like those found on Reddit’s r/AskComputerScience, specifically NetworkChuck’s YouTube channel, offer excellent introductory material.
This section will explore the core concepts, beginning with defining what constitutes a network and outlining its significant benefits. We’ll delve into the essential hardware and software components that make networks function, laying the groundwork for more advanced topics. A solid grasp of these basics, as emphasized by CETPA Infotech’s resources, is paramount for anyone pursuing Network+ certification and beyond.
A. What is a Network?

A network is fundamentally a collection of interconnected devices capable of exchanging data and sharing resources. These devices, ranging from computers and smartphones to servers and printers, communicate using a common set of rules, or protocols. This interconnectedness allows for collaboration, information access, and efficient resource utilization.
Networks aren’t simply about physical connections; they also encompass the logical relationships between devices. Resources like NetworkChuck’s YouTube channel, highlighted on r/AskComputerScience, effectively illustrate these concepts. Understanding network architecture, whether a simple home network or a complex enterprise system, begins with recognizing this fundamental principle of interconnected communication.
B. Network Benefits & Importance
Networks deliver substantial benefits, fundamentally transforming how we live and work. Resource sharing – files, printers, internet access – boosts efficiency and reduces costs. Communication is streamlined through email, instant messaging, and video conferencing, fostering collaboration. Centralized data management enhances security and simplifies backups.
The importance of networks is amplified in today’s digital world. Businesses rely on them for operations, and individuals depend on them for information and entertainment. Resources like those from CETPA Infotech, mentioned alongside NetworkChuck on Reddit, emphasize the growing need for skilled networking professionals. Networks are no longer a convenience; they are a critical infrastructure.
C. Network Components: Hardware & Software
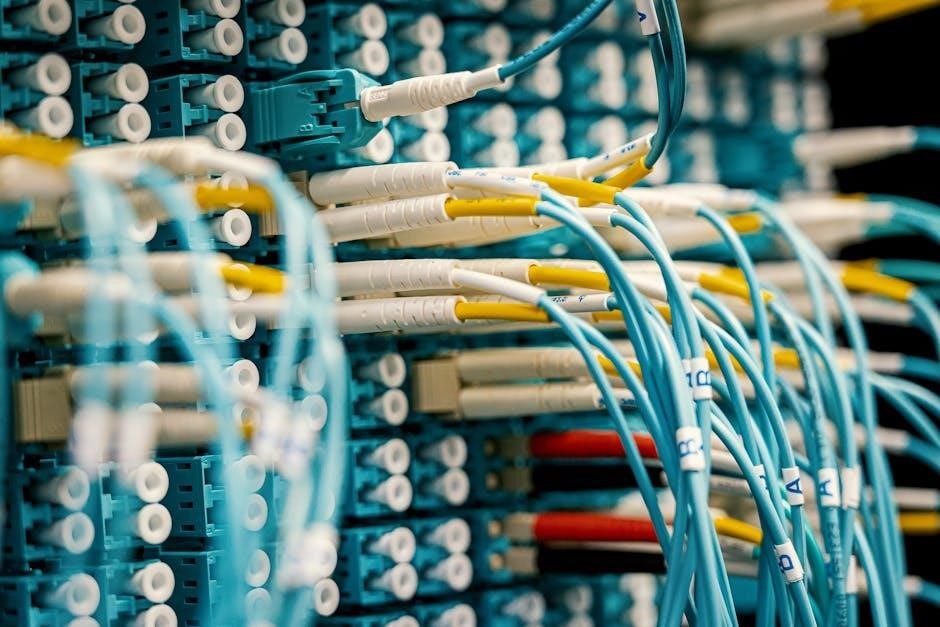
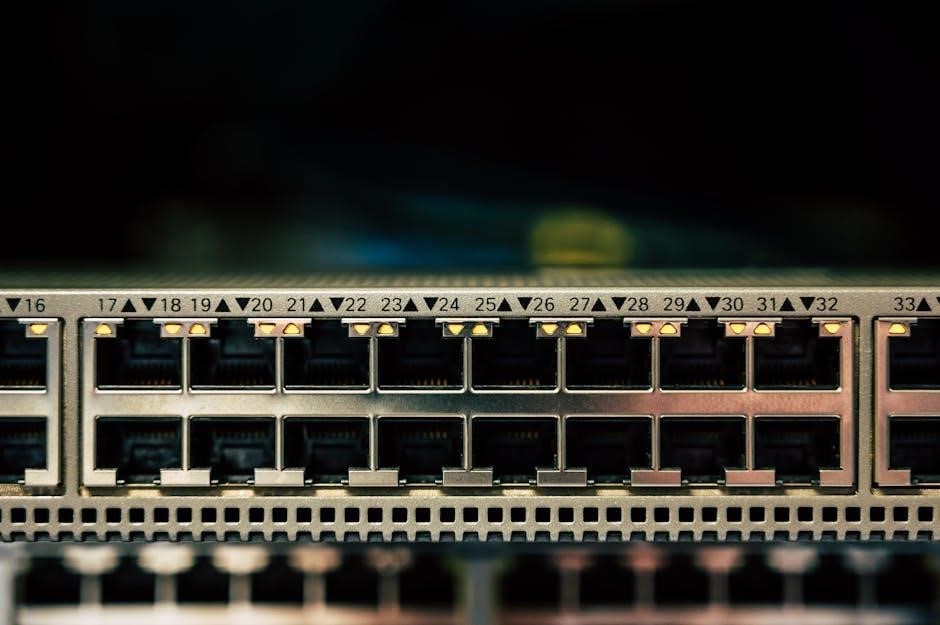
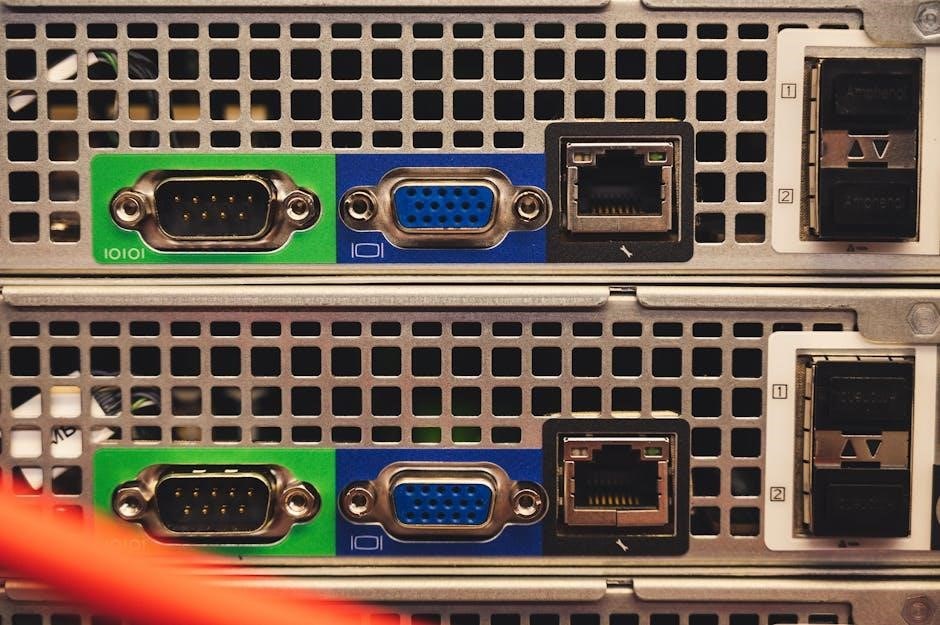
Networks comprise both physical hardware and essential software. Hardware includes devices like routers, switches, and network interface cards (NICs) which facilitate connectivity. Cabling – Ethernet or fiber optic – transmits data. Wireless access points enable Wi-Fi connections. Servers provide centralized resources and services.
Software is equally crucial. Network operating systems (NOS) manage network functions. Protocols, like those discussed in learning resources, define communication rules. Applications leverage the network for data transfer and interaction. Understanding both hardware and software is vital, as highlighted by comprehensive courses like those found on NetworkChuck’s YouTube channel, for effective network administration.
II. Network Models: The Foundation of Communication
Network models provide a conceptual framework for understanding how data travels across networks. The two primary models are the OSI (Open Systems Interconnection) and TCP/IP models. The OSI model, a seven-layer structure, details each stage of communication, from physical transmission to application interaction.
The TCP/IP model, the practical standard for the internet, consolidates some OSI layers. Grasping these models is fundamental, as they explain how protocols function and interact. Resources like those offered by CETPA Infotech can aid in visualizing these complex structures, providing a solid base for network troubleshooting and design.
A. OSI Model: A Layered Approach
The OSI model breaks down network communication into seven distinct layers: Physical, Data Link, Network, Transport, Session, Presentation, and Application. Each layer has a specific function, working in concert to ensure reliable data transfer. Understanding this layered approach is crucial for network professionals.
Troubleshooting becomes more efficient when you can pinpoint issues to a specific layer. While the TCP/IP model is dominant in practice, the OSI model remains a valuable conceptual tool. Resources like NetworkChuck’s videos can help visualize how data encapsulation and de-encapsulation occur as it moves through these layers.
Layer 1: Physical Layer
The Physical Layer is the foundation of network communication, dealing with the actual physical transmission of data. This layer defines characteristics like cabling standards (Ethernet, fiber optic), voltage levels, data rates, and physical connectors. It’s concerned with the “bits” themselves – how they are represented as signals.
Common components at this layer include network cables, hubs, and repeaters. Troubleshooting often involves checking cable integrity and signal strength. While seemingly simple, understanding the Physical Layer is vital as errors here directly impact all subsequent layers. Resources like those from CETPA Infotech can provide detailed insights into these physical aspects.
Layer 2: Data Link Layer
The Data Link Layer provides error-free transmission of data frames between two directly connected nodes. It’s responsible for physical addressing using MAC addresses, framing data into packets, and implementing access control methods to manage network access. This layer divides the data stream into manageable frames.
Key technologies at this layer include Ethernet and Wi-Fi. Switches operate primarily at Layer 2, forwarding frames based on MAC addresses. Error detection mechanisms, like checksums, ensure data integrity. Understanding the Data Link Layer is crucial for diagnosing connectivity issues within a local network segment, complementing learning from resources like NetworkChuck’s tutorials.
Layer 3: Network Layer
The Network Layer is responsible for logical addressing and routing data packets from source to destination across multiple networks. This layer utilizes IP addresses to identify devices and determines the best path for data transmission. Routers are the primary devices operating at this layer, forwarding packets based on IP addresses and routing tables.
Key protocols include IP (both IPv4 and IPv6) and ICMP. Fragmentation and reassembly of packets occur at this layer if necessary. Understanding concepts like subnetting, crucial for network efficiency, falls within the Network Layer’s domain. Resources like NetworkChuck can help solidify understanding of these complex, yet vital, networking principles.
Layer 4: Transport Layer
The Transport Layer provides reliable or unreliable data delivery between applications on different hosts. It segments data from the Application Layer and reassembles it at the destination. Two primary protocols operate here: TCP (Transmission Control Protocol) and UDP (User Datagram Protocol).
TCP offers connection-oriented, reliable transmission with error checking and flow control. UDP is connectionless and faster, but less reliable, suitable for applications like streaming. Port numbers are utilized at this layer to identify specific applications. Understanding the differences between TCP and UDP is fundamental to grasping network communication, and resources like NetworkChuck can aid in this comprehension.
B. TCP/IP Model: The Internet Standard
The TCP/IP model is the foundational communication language of the internet, a practical implementation derived from the more theoretical OSI model. It consists of four layers: Application, Transport, Internet, and Network Access. This model simplifies networking concepts for practical application.
Unlike the seven layers of OSI, TCP/IP focuses on interoperability. The Application layer encompasses protocols like HTTP and DNS. The Transport layer utilizes TCP and UDP for data delivery. The Internet layer handles IP addressing and routing. Finally, the Network Access layer deals with physical transmission. Resources like CETPA Infotech can provide deeper insights into this crucial model.
III. Network Topologies: Physical & Logical Arrangements
Network topology defines the physical or logical arrangement of devices on a network. Common topologies include Bus, Star, Ring, and Mesh, each offering unique advantages and disadvantages regarding cost, scalability, and fault tolerance.

A Bus topology uses a single cable, while a Star topology centralizes connections through a hub or switch. Ring topologies circulate data in one direction, and Mesh topologies provide redundant connections for high reliability. Understanding these arrangements is crucial for network design and troubleshooting. Choosing the right topology impacts network performance and maintenance, forming a core element of Network+ knowledge.
A. Bus Topology
The Bus topology utilizes a single cable, often coaxial, as the backbone to connect all devices. Data travels along this cable in both directions, requiring termination at each end to prevent signal reflection. This makes it simple and inexpensive to implement initially, but presents challenges.
A break in the cable disrupts the entire network. Troubleshooting can be difficult as identifying the fault location requires methodical testing. While historically significant, Bus topologies are rarely used in modern networks due to their limitations in scalability and reliability. Understanding its drawbacks is vital for Network+ certification, despite its declining prevalence.
B. Star Topology
The Star topology is the most common network arrangement today. It features a central hub or switch to which all devices connect. This centralized design offers significant advantages over older topologies like the bus. If one device fails, it doesn’t impact the rest of the network, enhancing reliability.
Troubleshooting is simplified as issues can be isolated to individual connections. However, the entire network relies on the central hub/switch; its failure brings down the whole system. Star topologies are easily scalable, allowing for the addition of new devices without disrupting existing connections, making it ideal for modern network infrastructure.
C. Ring Topology
The Ring topology connects devices in a circular fashion, with data traveling in one direction. Each device acts as a repeater, forwarding data to the next until it reaches its destination. While offering relatively simple implementation, ring topologies present challenges in modern networking.
A single point of failure exists; a break in the ring disrupts the entire network. Troubleshooting can be complex, as identifying the fault requires tracing the signal path. Though historically used, ring topologies are less common now due to their limitations in scalability and resilience compared to star or mesh configurations.
D. Mesh Topology
Mesh topology establishes numerous connections between devices, creating redundancy and high reliability. In a full mesh, every device connects directly to all others, while a partial mesh offers some, but not all, connections. This architecture excels in scenarios demanding constant uptime and fault tolerance.
However, mesh networks are complex and expensive to implement, requiring significant cabling and configuration. The sheer number of connections can make troubleshooting challenging. Despite these drawbacks, mesh topologies are valuable in critical infrastructure and wireless networks where uninterrupted connectivity is paramount, offering robust performance.
IV. Network Types: Categorizing Networks by Scale & Purpose
Networks are classified based on their geographical span and intended use. LANs (Local Area Networks) connect devices within a limited area, like a home or office, offering high speeds and resource sharing. WANs (Wide Area Networks) span larger distances, often utilizing public networks, connecting LANs across cities or countries.
MANs (Metropolitan Area Networks) bridge the gap, covering a city or large campus. PANs (Personal Area Networks) are the smallest, connecting devices around a single user, like Bluetooth headsets. Understanding these distinctions is crucial for designing and managing networks effectively, tailoring solutions to specific needs and scales.
A. LAN (Local Area Network)
Local Area Networks (LANs) are foundational to modern connectivity, typically confined to a single building or campus. They prioritize high-speed data transfer and resource sharing among connected devices. Common technologies include Ethernet and Wi-Fi, enabling seamless communication.
LANs are characterized by their private ownership and administration, offering greater control over security and performance. They are essential for homes, offices, and schools, facilitating file sharing, printer access, and internet connectivity; Understanding LAN infrastructure is vital for network troubleshooting and optimization, forming the core of many network environments.
B. WAN (Wide Area Network)
Wide Area Networks (WANs) extend beyond geographical limitations, connecting LANs across cities, countries, or even globally. Unlike LANs, WANs typically utilize public infrastructure like telecommunication lines and the internet. Technologies such as MPLS, leased lines, and VPNs facilitate secure and reliable data transmission over vast distances.
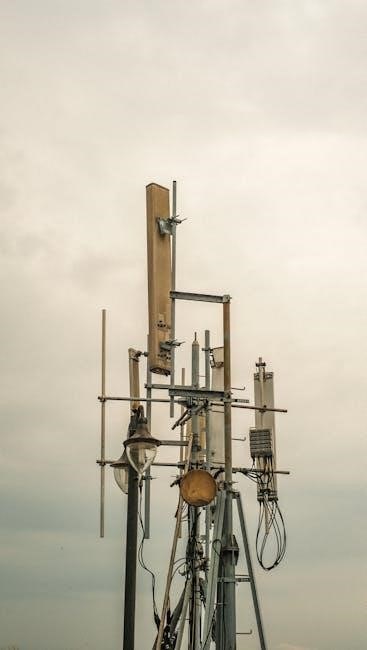
WANs are crucial for businesses with multiple locations, enabling centralized data management and remote access. They often involve higher costs and more complex configurations than LANs due to their scale and reliance on external providers. Understanding WAN concepts is essential for network professionals managing distributed networks and ensuring seamless connectivity.

C. MAN (Metropolitan Area Network)
Metropolitan Area Networks (MANs) bridge the gap between LANs and WANs, typically covering a city or large campus. They are larger than a LAN but smaller than a WAN, offering high-speed connectivity to multiple LANs within a defined metropolitan area. MANs often utilize technologies like fiber optics to deliver robust performance.
Common applications include connecting government buildings, universities, and business districts. MANs provide a cost-effective solution for organizations needing to share resources and data across a city-wide footprint. They offer greater bandwidth and lower latency compared to WANs for local communications, making them ideal for data-intensive applications.
D. PAN (Personal Area Network)
A Personal Area Network (PAN) is the smallest and most basic type of network, designed for connecting devices within a person’s immediate vicinity – typically a few meters. These networks center around an individual and their personal devices, facilitating communication between them.
Common examples include Bluetooth connections between a smartphone and wireless headphones, or a laptop connecting to a wireless mouse. PANs often utilize technologies like Bluetooth, infrared, or USB to establish connections. They are characterized by low power consumption and limited range, focusing on convenience and personal device integration. Security is a key consideration within PANs, given their close proximity to the user.
V. Network Addressing: Identifying Devices on a Network
Network addressing is fundamental to communication, enabling devices to locate and interact with each other. This involves assigning unique identifiers to each device on a network. Two primary addressing schemes are crucial: IP addressing and MAC addressing.
IP (Internet Protocol) addresses – both IPv4 and the newer IPv6 – provide logical addresses used for routing data across networks. MAC (Media Access Control) addresses are physical addresses hardcoded into network interface cards (NICs). Subnetting, a key component, divides larger networks into smaller, more manageable segments, improving efficiency and security. Understanding these addressing methods is vital for network troubleshooting and configuration.

A. IP Addressing: IPv4 & IPv6
IP addressing is the cornerstone of network communication, assigning logical addresses to devices. IPv4, the established standard, utilizes 32-bit addresses, facing exhaustion due to the proliferation of internet-connected devices. These addresses are represented in dotted decimal notation (e.g., 192.168.1.1).
IPv6, the successor, employs 128-bit addresses, offering a vastly larger address space. Represented in hexadecimal notation, IPv6 addresses alleviate the limitations of IPv4. Transitioning to IPv6 is crucial for future network scalability. Both protocols facilitate routing packets across networks, but IPv6 offers enhanced features like auto-configuration and improved security.
B. Subnetting: Dividing Networks for Efficiency
Subnetting is a vital technique for optimizing network performance and security. It involves logically dividing a larger network into smaller, more manageable subnetworks. This process enhances efficiency by reducing network congestion and broadcast traffic within each subnet.
By strategically allocating IP address ranges, subnetting improves network organization and simplifies administration. It also strengthens security by isolating sensitive resources within specific subnets. Understanding subnet masks is crucial for defining network boundaries and determining the number of usable host addresses within each subnet. Effective subnetting is key to scalable and secure network design.
C. MAC Addressing: Physical Device Identification
MAC (Media Access Control) addresses are unique identifiers assigned to network interfaces, functioning as a physical address for devices. These 48-bit hexadecimal addresses are burned into the Network Interface Card (NIC) by the manufacturer, ensuring hardware-level identification.
Unlike IP addresses which can change, MAC addresses are generally static, providing a permanent identifier. They are crucial for communication within a local network segment, enabling devices to locate each other directly. Data packets utilize MAC addresses for delivery on the data link layer. Understanding MAC addresses is fundamental for network troubleshooting and security measures like MAC filtering.
VI. Network Protocols: Rules for Communication
Network protocols are the standardized rules governing data communication, ensuring devices can understand each other. TCP (Transmission Control Protocol) provides reliable, connection-oriented communication, guaranteeing delivery and order of data packets – essential for applications like web browsing.
UDP (User Datagram Protocol) offers faster, connectionless communication, prioritizing speed over reliability, suitable for streaming and online gaming. HTTP/HTTPS are the foundations of web data transfer, with HTTPS adding encryption for secure communication. DNS (Domain Name System) translates human-readable domain names into IP addresses, enabling easy access to online resources.
A. TCP (Transmission Control Protocol)

TCP is a connection-oriented protocol, establishing a dedicated connection before data transfer, ensuring reliable communication. It utilizes a three-way handshake to synchronize and acknowledge data packets, guaranteeing delivery and correct order. TCP provides error checking and recovery mechanisms, retransmitting lost packets to maintain data integrity.
Flow control prevents a fast sender from overwhelming a slow receiver, while congestion control manages network traffic to avoid bottlenecks. Applications like web browsing, email, and file transfer rely on TCP’s reliability. Understanding TCP’s features is crucial for troubleshooting network issues and optimizing application performance.
B. UDP (User Datagram Protocol)
UDP is a connectionless protocol, offering a faster but less reliable data transmission method compared to TCP. It doesn’t establish a dedicated connection, simply sending data packets without guaranteed delivery or order. UDP lacks error recovery mechanisms, making it suitable for applications where speed is prioritized over accuracy.
Applications like online gaming, video streaming, and DNS often utilize UDP due to its low overhead. While packets may be lost or arrive out of sequence, the speed compensates for these drawbacks. UDP’s simplicity makes it efficient for broadcasting and multicasting data to multiple recipients simultaneously, proving valuable in specific network scenarios.
C. HTTP/HTTPS (Web Protocols)
HTTP (Hypertext Transfer Protocol) is the foundation of data communication on the World Wide Web. It defines how messages are formatted and transmitted between clients (like web browsers) and servers. HTTP operates on a request-response cycle, where clients request resources, and servers respond with the requested data.
HTTPS (HTTP Secure) is the secure version of HTTP, utilizing encryption to protect data in transit. HTTPS employs SSL/TLS protocols to establish a secure connection, safeguarding sensitive information like passwords and credit card details. The “S” signifies a secure, encrypted connection, crucial for e-commerce and any website handling personal data. Browsers indicate HTTPS connections with a padlock icon.
D. DNS (Domain Name System)
DNS (Domain Name System) functions as the internet’s phonebook, translating human-readable domain names (like google.com) into machine-readable IP addresses (like 172.217.160.142). This translation process is essential because computers communicate using IP addresses, not domain names.
When you type a domain name into your browser, a DNS server is queried to find the corresponding IP address. This process involves a hierarchical structure of DNS servers, starting with root servers and cascading down to authoritative name servers. DNS caching improves efficiency by storing recently resolved IP addresses, reducing lookup times and network traffic. Without DNS, navigating the internet would be significantly more complex.
VII. Network Security Basics
Network security is paramount in today’s interconnected world, protecting valuable data and systems from unauthorized access and malicious attacks. Firewalls act as the first line of defense, controlling network traffic based on predefined security rules, blocking potentially harmful connections.
Encryption secures data transmission, rendering it unreadable to unauthorized parties. Common threats include malware, phishing, and denial-of-service attacks. Implementing strong passwords, regularly updating software, and employing intrusion detection systems are crucial security measures. Understanding vulnerabilities and proactively mitigating risks are essential components of a robust network security posture.
A. Firewalls: Protecting Network Boundaries
Firewalls are essential network security devices that control incoming and outgoing network traffic based on predetermined security rules. They act as a barrier between a trusted internal network and untrusted external networks, such as the internet.
Firewalls can be hardware-based, software-based, or a combination of both. They inspect network packets and block those that don’t meet specified criteria. Different types of firewalls exist, including packet-filtering firewalls, stateful inspection firewalls, and next-generation firewalls, offering varying levels of protection. Properly configured firewalls are crucial for preventing unauthorized access and mitigating network threats.
B. Encryption: Securing Data Transmission
Encryption is a fundamental security process that converts readable data (plaintext) into an unreadable format (ciphertext) to protect its confidentiality. This scrambled data can only be deciphered back into plaintext with a decryption key.
Encryption is vital for securing data transmitted across networks, especially public networks like the internet. Common encryption protocols include SSL/TLS (used for HTTPS) and VPNs. Symmetric encryption uses the same key for encryption and decryption, while asymmetric encryption uses a key pair – a public key for encryption and a private key for decryption. Strong encryption is essential for protecting sensitive information from interception and unauthorized access.
C. Common Network Threats & Vulnerabilities
Networks face numerous threats, including malware (viruses, worms, Trojans), phishing attacks attempting to steal credentials, and denial-of-service (DoS) attacks disrupting network availability. Ransomware encrypts data and demands payment for its release, posing a significant risk.
Vulnerabilities often stem from weak passwords, unpatched software, and misconfigured firewalls. Man-in-the-middle attacks intercept communication, while SQL injection targets databases. Regularly updating security software, implementing strong access controls, and educating users about security best practices are crucial for mitigating these risks and maintaining a secure network environment.
